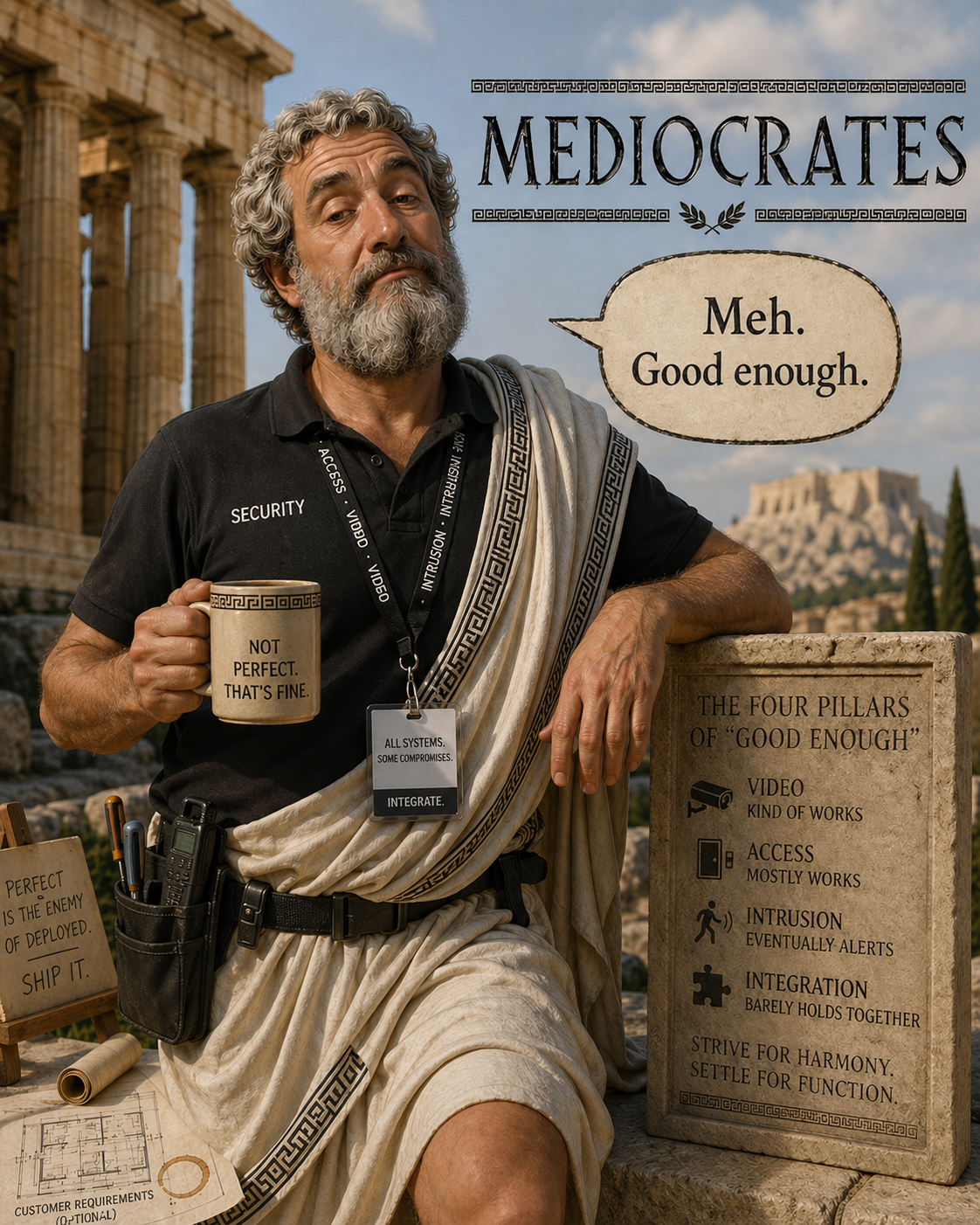
The Hidden Cost of 'Good Enough' - How minimal effort in Security Risk Management leads to accumulated risk
There is a particular kind of organisational risk that rarely announces itself. It does not arrive in the form of a crisis, a breach, or a visible failure. It accumulates quietly, lodged in the gap between security that is sufficient on paper and security that is genuinely fit for purpose. It lives in the access card that should have been deactivated six months ago, in the visitor management log that no one has reviewed since the system was installed, in the risk register entry that was closed as 'mitigated' because a measure was implemented rather than because the underlying risk was resolved.
This is the hidden cost of 'good enough': not a single catastrophic event, but the compounding accumulation of deferred decisions, under-resourced controls, and reviews that are conducted more for compliance than comprehension. Across organisations of all sizes and sectors, the tendency to treat security as a threshold to be met rather than a discipline to be maintained creates conditions in which risk grows unobserved, unchallenged, and, eventually, unmanageable.
Understanding why this happens, and what it truly costs, is the starting point for any organisation serious about its long-term security posture.
The Logic of Deferral
Security investment decisions are rarely made in isolation. They compete with operational priorities, capital projects, staffing pressures, and the ever-present tendency to direct resources toward problems that are visible and immediate rather than risks that are latent and probabilistic. In this environment, security measures that are 'already in place' are easy to deprioritise. The locks are on the doors. The cameras are recording. The policies have been written. What more is needed?
This reasoning is seductive precisely because it contains a partial truth. Baseline measures do provide a degree of protection. A building without access control is meaningfully more vulnerable than one with it. But the question that rarely gets asked is whether the controls in place are still calibrated to the current threat environment, still functioning as intended, and still addressing the risks for which they were originally designed.
Physical security controls degrade over time, not only through mechanical wear, but through organisational change. A building occupied by fifty staff presents a different access control challenge from the same building occupied by two hundred. A site that once housed administrative functions and now accommodates sensitive research has different perimeter requirements. When controls are not revisited in light of these changes, the gap between perceived protection and actual protection widens, often without anyone noticing.
Deferred investment in security rarely stays deferred. It compounds.
The deferral logic is further reinforced when security reviews produce reassuring findings. This is not always a sign of good security; it is sometimes a sign of insufficient scrutiny. A review that confirms existing controls without testing their effectiveness, without tracing each measure back to a specific and current risk, and without examining whether residual risk remains acceptable is not a review in any meaningful sense. It is an exercise in validation rather than analysis.
Accumulated Risk Across Security Domains
The compounding nature of deferred security effort is most clearly visible when one examines how risk accumulates across the interconnected domains of physical security, personnel security, and information handling. These are not discrete silos. Weakness in one area routinely creates or amplifies vulnerability in another, and the most serious security failures are almost always the product of multiple accumulated gaps rather than a single catastrophic oversight.
Consider a scenario that is entirely plausible in any mid-sized organisation. A long-serving employee departs under difficult circumstances. The departure is managed poorly from a personnel security perspective: the exit interview is cursory, the leaver's knowledge of sensitive processes is not adequately documented, and the access deactivation process is delayed because the relevant system administrator is on leave. In the meantime, the former employee retains physical access to a secondary site via a card that was not included in the initial revocation request.
None of these failures, taken individually, would register as a significant security event. The exit interview policy exists; it was simply not followed rigorously. The access control system is functional; a procedural step was missed. But in combination, they create a window of genuine exposure. If that window coincides with a period during which sensitive procurement decisions are being made, or during which a contractual dispute with the departing employee is active, the accumulated risk becomes material.
Now consider what happens when this kind of accumulated weakness is not discovered and resolved but is instead carried forward, unexamined, into the next year's security review. The review, conducted against a checklist rather than a risk model, finds that access control is 'in place' and exit interview procedures 'exist'. The underlying vulnerabilities are not visible because the review is not designed to surface them.
This is how organisations arrive at a point of significant exposure having genuinely believed, at every stage, that their security was adequate. The cost is not the result of a decision to accept risk. It is the result of a failure to see it.
Physical Security: The Domain Most Prone to Complacency
Of all the security domains, physical security is perhaps the most susceptible to the 'good enough' fallacy. This is partly because its outputs are tangible and visible: doors have locks, fences are erected, cameras are mounted. The presence of these controls creates a psychological assurance that can be difficult to distinguish from genuine security. It is also because physical security failures, unlike information breaches, do not always generate the kind of discrete, reportable incident that triggers a formal response. A tailgating incident that goes unnoticed, a delivery area that is routinely unsupervised, a visitor who bypasses the sign-in process without challenge: these are not events that appear in incident logs. They are simply the background noise of inadequate security practice.
Effective physical security is not primarily about the presence of controls. It is about the coherent layering of those controls in a manner that reflects a considered understanding of the threat environment, the asset profile, and the realistic behaviour of both adversaries and staff. A sophisticated access control system that has never been tested for tailgating resistance, that lacks integration with personnel records, and that generates audit logs nobody reads is not providing the protection its specification suggests. It is providing the appearance of protection.
The same principle applies to security plans and threat assessments that are treated as static documents rather than living frameworks. A security plan written three years ago against a different occupancy profile, a different organisational structure, and a different threat environment may contain measures that are now redundant, controls that are no longer proportionate to current risks, and gaps that have emerged as the organisation has evolved. Without systematic review, these plans accumulate irrelevance while continuing to provide the comfort of apparent compliance.
The protective security frameworks developed across a range of jurisdictions, including New Zealand's own established guidance, consistently emphasise that physical security controls must be underpinned by a clear understanding of what is being protected, from whom, and why. The value of that framing is not merely conceptual. It provides the analytical structure that allows each control to be evaluated against a specific risk, and it creates accountability for residual risk that cannot be mitigated. Without this structure, security decisions become habitual rather than deliberate, and the accumulated cost of that habit is borne quietly, until it is not.
Personnel Security and the Insider Dimension
Personnel security occupies an uncomfortable space in most organisational risk frameworks. It requires organisations to think carefully about the people they employ and trust, and to put in place measures that can feel, in a culture of collegiality and openness, vaguely at odds with the working environment they are trying to maintain. This discomfort is understandable, but it is also costly.
The insider threat is not an exotic or remote risk. It is the most statistically prevalent source of significant security incidents across most sectors. It encompasses not only deliberate betrayal but the far more common scenario of well-intentioned staff who do not understand the security implications of their actions: the employee who removes sensitive documents to work from home, the contractor who discusses client arrangements in a public space, the new starter who is not adequately briefed on information handling expectations and therefore defaults to the habits of their previous employer.
Addressing this risk requires more than a pre-employment screening process and an annual security awareness reminder. It requires a sustained and proportionate approach to understanding who has access to sensitive assets, what their circumstances are, and whether the controls governing that access remain appropriate. This is not surveillance; it is risk management. And it is the kind of risk management that, when deferred or treated as a compliance exercise, creates conditions that can be exploited or that can produce inadvertent harm at considerable cost to the organisation.
When personnel security is integrated with physical security in a coherent framework, the resulting controls are both more effective and more defensible. Access privileges are connected to role and need. Departures trigger a consistent and complete revocation process. Sensitive areas are occupied only by those whose access has been properly authorised and reviewed. When these elements operate independently, the gaps between them become the vulnerabilities.
The Quality of the Review Matters as Much as the Frequency
One of the less visible dimensions of the 'good enough' problem is the quality of security reviews themselves. In a market where security consulting is offered across a wide spectrum, from highly methodical and analytically rigorous processes to commercially expedient checklist exercises, the outputs vary enormously. An organisation that commissions a review and receives a report is not necessarily better informed about its actual risk position. It depends entirely on whether the review process was designed to surface genuine risk or to confirm pre-existing assumptions.
A methodologically rigorous security review is characterised by a clear analytical framework in which every identified control is traced back to a specific risk, and every identified risk is assessed against a consistent and transparent criteria. It involves direct observation and testing of controls, not merely documentation review. It examines the interface between physical security, personnel arrangements, and information handling, rather than treating each in isolation. It produces findings that are genuinely prioritised by risk severity rather than arranged according to operational convenience. And it includes an honest assessment of residual risk, including the risks that cannot be fully mitigated within reasonable constraints.
This kind of review takes time and expertise. It requires analysts who understand not only the technical dimensions of security controls but the organisational dynamics that determine whether those controls function as designed. It requires independence from commercial pressures that might otherwise encourage a preference for findings that are reassuring rather than accurate.
The alternative, a review that proceeds quickly, that relies heavily on staff self-reporting, that applies a generic framework without adapting it to the specific risk profile of the organisation, and that produces a set of findings lacking clear traceability to the threat environment, may satisfy an audit requirement. It will not, however, serve the organisation's genuine security interests. In fact, it may actively undermine them by creating a false sense of assurance that defers necessary investment even further.
An organisation that commissions a review and receives a report is not necessarily better informed about its actual risk position.
When Deferred Investment Becomes Unavoidable Cost
The moment at which deferred security investment typically becomes unavoidable is not, in most cases, a security incident. It is a trigger event of a different kind: a change in tenancy that requires a new security assessment as a condition of the lease, a major contract that requires the organisation to demonstrate security credentials to a client or partner, a regulatory change that introduces new obligations around access management or personnel vetting, or an insurance review that identifies security arrangements as materially inadequate.
At this point, the organisation discovers that the cost of addressing accumulated gaps is significantly higher than it would have been had those gaps been addressed progressively. Physical infrastructure that could have been upgraded incrementally now requires wholesale replacement. Personnel security processes that could have been embedded gradually now require urgent, disruptive implementation. A security plan that could have been maintained as a living document now requires a comprehensive rewrite against a current threat environment that differs significantly from the one in which the original was drafted.
There is also a less tangible but equally real cost: the time and management attention required to address accumulated risk under pressure is substantially greater than the time required to manage risk in a structured, continuous fashion. The organisation that has maintained a current, coherent security framework will typically respond to the trigger event in a matter of weeks. The organisation that has deferred and accumulated will spend months in a process that is costly, disruptive, and, in many respects, avoidable.
This dynamic is well understood in comparable disciplines. Deferred maintenance in facilities management, deferred calibration in quality assurance, deferred governance in financial management: the pattern is consistent. Short-term savings generate medium-term accumulation and long-term cost. Security is not different. It simply tends to be less visible until it is not.
A Structured Approach as the Only Sustainable Response
The response to accumulated security risk is not, in the first instance, a major investment in new controls. It is a structured, honest assessment of where the organisation actually stands: what risks are present, what controls are in place, whether those controls are effective, and what the gap between current exposure and acceptable risk looks like when examined clearly.
This kind of assessment, conducted by analysts with both the technical competence to evaluate controls and the independence to report findings without regard for organisational comfort, is the essential starting point. It creates the visibility that makes informed decision-making possible. It generates a prioritised, risk-linked programme of improvement that allows investment to be directed where it will have the greatest effect. And it produces a baseline against which future reviews can be meaningfully measured.
From that foundation, organisations can build a security framework that is genuinely proportionate to their risk profile, that evolves as the organisation and its threat environment evolve, and that allows security investment to be managed as a continuous and deliberate programme rather than a series of reactive responses to accumulated pressure.
The goal is not perfection. No security framework eliminates risk, and the pursuit of zero risk is neither achievable nor desirable. The goal is clarity: a clear understanding of what risks exist, what is being done to manage them, what residual risk remains, and what the cost of that residual risk is to the organisation. That clarity is the foundation on which genuinely effective security is built. It is also, not incidentally, the most effective counter to the slow and silent accumulation of risk that characterises the 'good enough' approach.
Organisations that invest in this kind of rigour tend to discover something counterintuitive: structured security management is often less expensive over time than the alternatives, not because it eliminates all risk, but because it eliminates the far greater cost of managing risk under pressure, without adequate information, and against a backdrop of accumulated decisions that were never quite adequate to begin with.
About ICARAS
ICARAS is a New Zealand-based security risk management consultancy providing independent, expert-led analysis across physical security, personnel security, information security, and crisis planning. Our assessments are grounded in established protective security principles and tailored to the specific risk profile of each organisation we work with.
Visit us at www.icaras.nz